AI-Driven Cyber Defense & Pentesting
We provide continous AI-based security and dark web monitoring with certified PenTesting reports, ready for compliance: SOC 2 Type II, ISO 27001, NIS2, etc.
We provide continous AI-based security and dark web monitoring with certified PenTesting reports, ready for compliance: SOC 2 Type II, ISO 27001, NIS2, etc.

Watch our demo video to discover how CyberTested's AI-driven platform protects your business from cyber threats 24/7.



Our automated software continuously scans your websites, emails and servers for vulnerabilities, malware, and compliance risks—helping you stay secure, compliant, and worry-free.
Ai-Based Automated Pen testing solution for your applications. Find all the issues in advance instead of users complaining about them.
Track leaked credentials, data breaches, threat actor discussions, and exploit marketplaces to stay ahead of potential security incidents.
Cybertested scanner will check the website for known malware, viruses, blacklisting status, website errors, out-of-date software, and malicious code.
Provide comprehensive training on threat awareness, secure practices, and incident response to build a security-conscious culture across your organization.
Identify vulnerable users, measure susceptibility to social engineering attacks, and provide targeted training to reduce security risks from email-based threats.
Navigate compliance requirements. Establish robust security controls, maintain audit-ready documentation, and demonstrate adherence to SOC2 and ISO 27001 standards.
Our team maintains the highest industry standards through continuous certification and training
Offensive Security Certified Professional - Advanced penetration testing certification
Certified Information Systems Security Professional - Industry gold standard
Expert Web Application Penetration Tester Certification. XSS, SQLi, RCE, etc.
Certified Information Security Manager - Information security management
Lead Auditor - Information security management systems
Security Operations Center · CompTIA · Security Information
Certified AI Machine Learning Professional by SecOps Group
Advanced OPSEC tactics and defence bypass strategies
The average cost of data breaches for company in 2022 is $150 Million. Over 100,000 folders are open to everyone in 88% of companies with over 1 million folders.
$10.5 Trillion global costs of cybercrime according to experts prediction by 2025. About 14 Billion data records had been lost or stolen up until 2019.
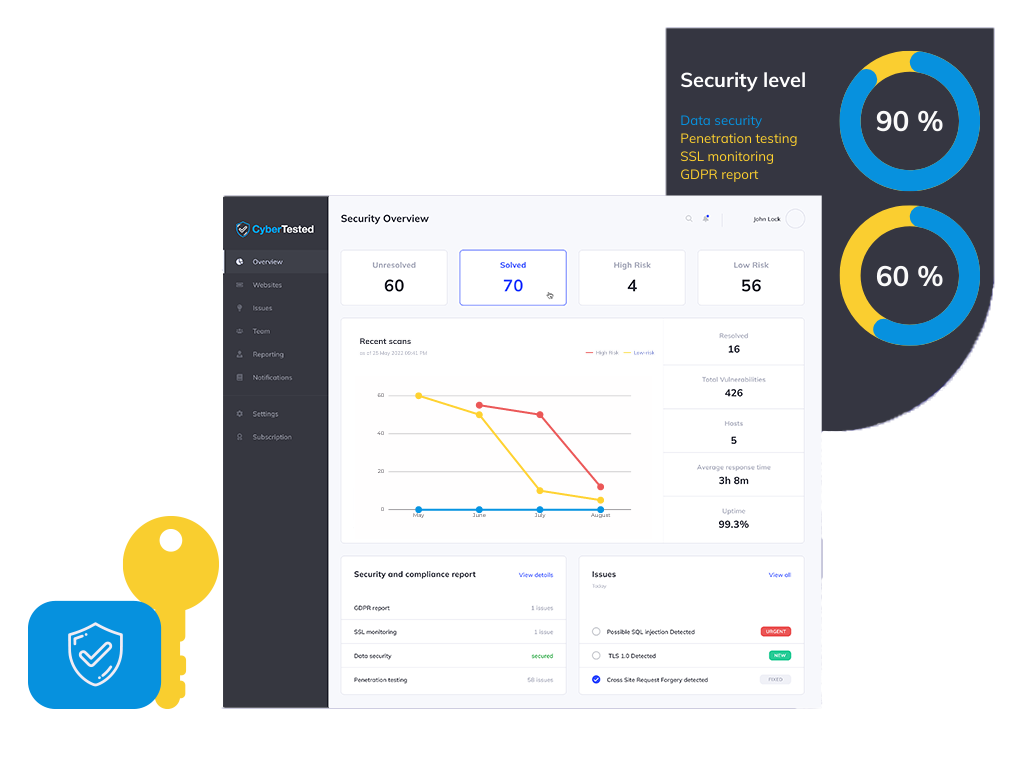
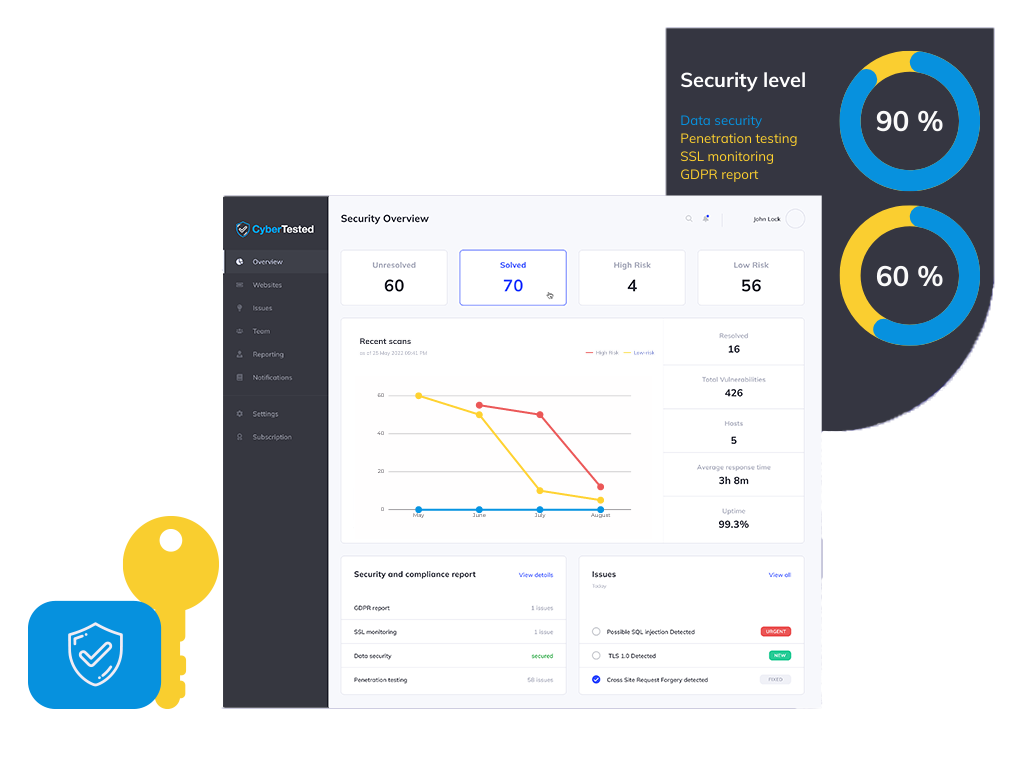
We introduce software that scans the vulnerabilities of websites, mobile applications, and cloud server equipment. With the help of this software, we will check SQL injection, XSS, GDPR compliance, incorrect configurations, and other security issues.
An automatic penetration test, supported by artificial intelligence (AI), will be carried out 24/7, on the basis of which periodic reports will be generated, each time including instructions for debugging!
The penetration report and test will be performed in accordance with the OWASP penetration guidelines under the supervision of our experts. With these techniques, we provide a unique insight into security risks that are often overlooked.
We take into account good practices of international standards PCI DSS 3.2, ISO / IEC 27001: 2013, ISO / IEC 27002: 2013 and ISO / IEC TR 27008 : 2011.


Find weaknesses in your most exposed systems and satisfy compliance needs. Choose the right cyber security solution.
Our solution will scan your website 24/7 and generate security and compliance reports to identify cyber threats.
Our solution will scan your website 24/7 and generate security and compliance reports to identify cyber threats.
The vulnerability remediation process is a workflow that fixes or neutralizes detected weaknesses.